KNOW, is our news aggregator and threat intel platform that collates the hottest news in cybersecurity and categorizes them accordingly. One of the most trending stories in this space happens to be about the Molerats espionage campaign in the Middle East.
Aliases: Gaza Hackers Team, Gaza Cyber gang, and Moonlight.
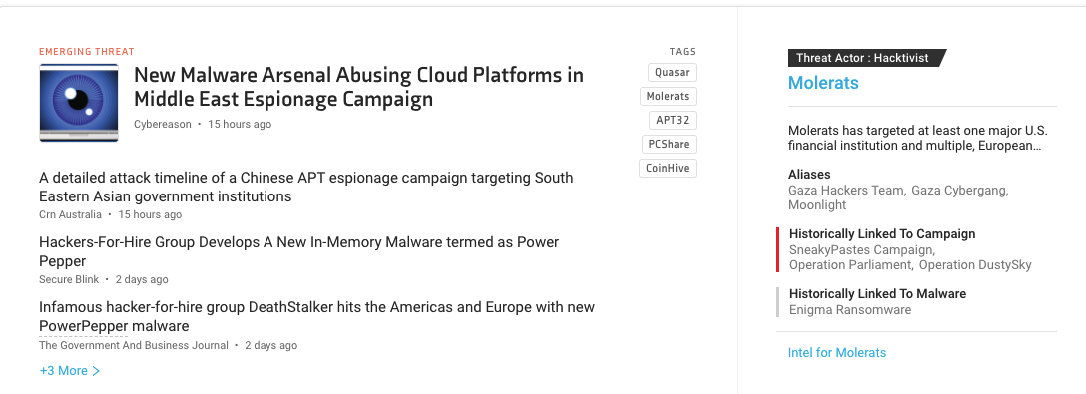
Molerats espionage campaign details
Security researchers have identified new espionage tools developed by Molerats. The tools include two new backdoors SharpStage and DropBook, as well as the MoleNet downloader. These tools together allow the attackers to execute malicious code and steal sensitive data from the infected computers.
The tools use of The DropBook backdoor uses fake Facebook accounts or Simplenote for command and control (C2), and both SharpStage and DropBook abuse a Dropbox client to exfiltrate stolen data as well as for storing their espionage tools.
Victims are lured in via political phishing themes such as Israeli-Saudi relations, Hamas elections, and other regional political events. As you can tell, the operation has been primarily observed in the Middle East. These new backdoors have been used before in conjunction with the Spark backdoor previously attributed to Molerats.
Twitter reacts to Molerats and Middle East espionage
#1 Nocturnus
Our new research is OUT! @Cybereason discovered a new #malware arsenal used by the #MoleRATs APT group (aka Gaza Cybergang). The newly discovered tools abuse cloud platforms such as #Dropbox #Facebook #Simplenote to carry out cyber #espionage attacks in the Middle East. pic.twitter.com/BzZEvUmrbD
— Cybereason_Nocturnus (@CR_Nocturnus) December 9, 2020
#2 CTech
.@Cybereason concluded that the campaign operators sought to target high ranking political figures and government officials in the Middle East.#Hack #CyberSecurity #MiddleEast https://t.co/MLG8lbXUuR
— CTech (@Calcalistech) December 9, 2020
#3 Virus Bulletin
Palo Alto Networks' Unit 42 team have looked at new targeted phishing campaigns by the Molerats group (a.k.a. Gaza Cybergang) that delivered the Sparks backdoor https://t.co/V72GR6Kok6 pic.twitter.com/sm9iV2jYDQ
— Virus Bulletin (@virusbtn) March 5, 2020
Molerats references from KNOW
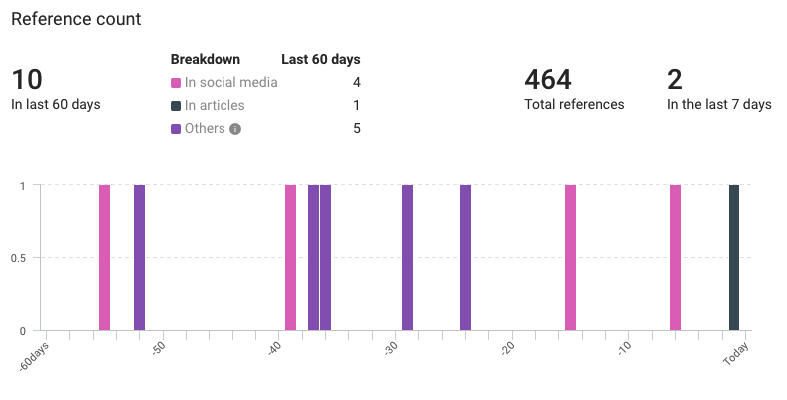
- Total references: 464
- Previous 60 days: 10
- Last 7 days: 2
Molerats context from KNOW
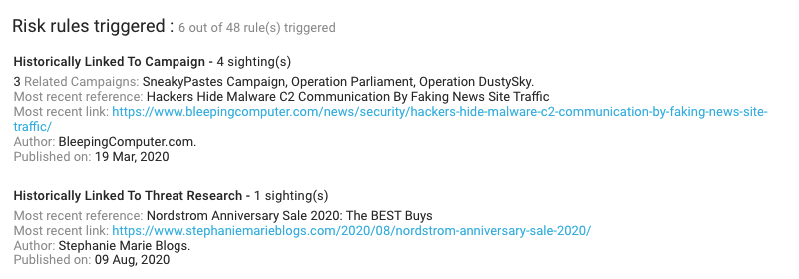
- Risk rules triggered: 6 out of 48
- Related campaigns: SneakyPastes Campaign, Operation Parliament, and Operation DustySky.
- Used intrusion methods: Phishing Campaign, Infection chain, Zero Day, Spear Phishing, and Social Engineering.
- Most recent sandbox reference: Hybrid Analysis result for ‘[UTW]_Fate_Apocrypha_-_10_[h300-720p][E21730DF].mkv.exe’
- Malware: Enigma ransomware
- Industries: Telecommunications, Retail, and Insurance.
- Hashes: 42
KNOW and protect yourself from Molerats

KNOW is not just a news aggregator but it also happens to be a threat intel dashboard. It is designed to help you get all the relevant insights from the global threat landscape.
Your SecOps and IT Ops teams work tirelessly to fix every security loophole, yet adversaries manage to go through. It is challenging to identify the relevant threats from the thousands that pop in every now and then. Here’s what Netenrich adds to the security landscape.
Netenrich’s Resolution Intelligence® uses a combination of threat and attack surface intelligence that effectively addresses the following pain points:
- Firstly, your organization’s attack surface is growing faster than your SecOps team and budget.
- Threat actors can see exposed assets that lie outside your security’s purview.
- There is a severe lack of talent and skill gaps are getting wider than ever before.
- Attacks are more frequent and it only takes one to inflict severe, irreversible damage on your organization and business reputation.
Would you like to stay up to date with the trending threats and empower your SecOps team?
Latest Threats Intel
What exactly is resolution intelligence, and what will it do for you?
Quick Sneak Peek
Subscribe To Our Newsletter!
The best source of information for Security, Networks, Cloud, and ITOps best practices. Join us.
Thank you for subscribing!




